Class 10 Computer Science Chapter 1 Introduction To Computer Network Question Answer, SEBA Class 10 Computer Science Solutions to each chapter is provided in the list so that you can easily browse through different chapters SCERT Class 10 Computer Science Chapter 1 Introduction To Computer Network and select needs one.
Class 10 Computer Science Chapter 1 Introduction To Computer Network
Also, you can read the SCERT book online in these sections Solutions by Expert Teachers as per SCERT (CBSE) Book guidelines. NCERT Solution of Class 10 Computer Science Chapter 1 Introduction To Computer Network is part of AHSEC All Subject Solutions. Here we have given Class 10 Computer Science Chapter 1 Introduction To Computer Network Notes for All Subjects, You can practice these here in Class 10 Computer Science.
Introduction To Computer Network
Chapter – 1
COMPUTER SCIENCE
TEXTUAL QUESTIONS AND ANSWERS
I. FILL IN THE BLANKS:
1. The hostname command is used to display_____.
Ans. Name of the computer.
2. The length of a IPv4 and a IPv6 is____and___.
Ans. 32 bit; 128 bit.
3. An access point is used to connect_____.
Ans. Wireless network.
4. The ping command is used to verify____.
Ans. The connectivity between two computers.
5. HTTPS transfer______data.
Ans. Encrypted.
II. MULTIPLE CHOICE QUESTIONS:
1. Which device is required to connect multiple heterogeneous networks?
(A) Hub
(B) Switch
(C) Router
(D) Access Point
Ans. (C) Router.
2. Which is the largest type of computer network?
(A) PAN
(B) LAN
(C) MAN
(D) WAN
Ans. (D) WAN.
3. Which protocol transfers encrypted data instead of plain data?
(A) HTTP
(B) HTTPS
(C) FTP
(D) SMTP
Ans. (B) HTTPS.
4. How many bytes are reserved for OUI in a MAC address?
(A) 3
(B) 8
(C) 24
(D) 12
Ans. (C) 24.
5. IP address can be automatically assigned if the network is connected with
(A) Access Point
(B) Mail Server
(C) Web Server
(D) DHPC Server
Ans. (D) DHPC Server.
III. SHORT ANSWER QUESTIONS:
1. Mention the names of components required to set up a MAN network. Draw a block diagram of a MAN network labeling the name of each component.
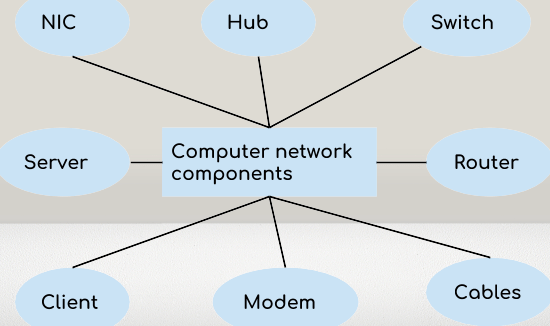
Ans. Computer network components are the major parts which are needed to install the software. Some important network components are a Network Interface card, Router, HUB, Switch, Repeater, Bridge, server, and Modem.
2. Why hostname should not be used to identify a computer in a computer network?
Ans. Hostname is not a reliable way to identify a computer network because a hostname can be changed easily, and multiple hosts can have the same hostname. Additionally, a single host can have multiple network interfaces, each with a different hostname.
3. Give five examples of valid and five examples of invalid IPv4 addresses.
Ans. A valid IPv4 address must be in the form of A.B.C.D, where A, B, C, and D are numbers from 0-255.
Valid IPv4 Addresses:
- 192.168.0.1
- 10.0.0.255
- 172.16.31.5
- 255.255.255.0
- 127.0.0.1
Invalid IPv4 Addresses:
- 256.0.0.1 (Octet value exceeds 255)
- 192.168.1 (Missing one octet)
- 172.32.0.256 (Both octet values exceed 255)
- 300.200.100.50 (All octet values exceed 255)
- 192.168.256.10 (One octet value exceeds 255)
4. Can we compare HTTP and FTP protocols? Mention their functionality.
Ans. HTTP is used to transfer web pages between a client and a server while FTP is used to transmit files among different hosts.
Comparison between HTTP and FTP:
| Sl. No. | HTTP | FTP |
| 1 | The term HTTP is a Hypertext Transfer Protocol. | The term FTP is a File Transfer Protocol. |
| 2 | It is the set of rules that how web pages are transferred on different computers over the internet. | It is the set of rules that permit the downloading and uploading the files on the computer over the internet. |
| 3 | We use HTTP for providing various web pages from the web browser to the web server. | The URLs that use the HTTP protocol begin with HTTP. |
| 4 | It uses Transmission Control Protocol and runs on TCP port 80. | It uses Transmission Control Protocol and runs on TCP port 20 and TCP port 21. |
| 5 | HTTP does not require authentication. | FTP requires a password. |
5. How many 16 port switches required to connect 31 computers in a network?
Ans. A 16-port switch can connect 16 computers together. To connect 31 computers in a network, we need either a larger switch or 2 numbers of 16 port switches.



Introduction to computer network
Very good and its too much helpful for class 10 students to get the question and answer
Very good and its too much helpful for class 10 students to get the question and answer